This article is published in the White Paper category.
Our life in our hands: this saying has become literally true thanks to the mobile penetration that characterises modern times, where mobile phones are a natural extension of our bodies. On one side, we have all the comfort and endless possibilities unlocked by these small devices; if we flip the coin, though, the other side hides the concerns related to privacy and protection of personal data.
So, while allowing the continuous search for networks to guarantee the “always-on” mode, the recent evolution of the mobile operating systems has released methods to keep the phone hidden until safe to disclose itself. The randomization of the MAC address is one of those techniques, and its effect on Crowd Analytics’ solutions has been troublesome ever since its adoption.
Let’s take a step back. A MAC address is a unique code assigned to a device on a network to distinctively identify it. More specifically, the WiFi MAC address is the identifier assigned to any device’s port using the WiFi protocol.
Mobile phones including iPhones and Android devices are using the WiFi probing protocol to detect nearby WiFi networks and improve the location accuracy of the phone.
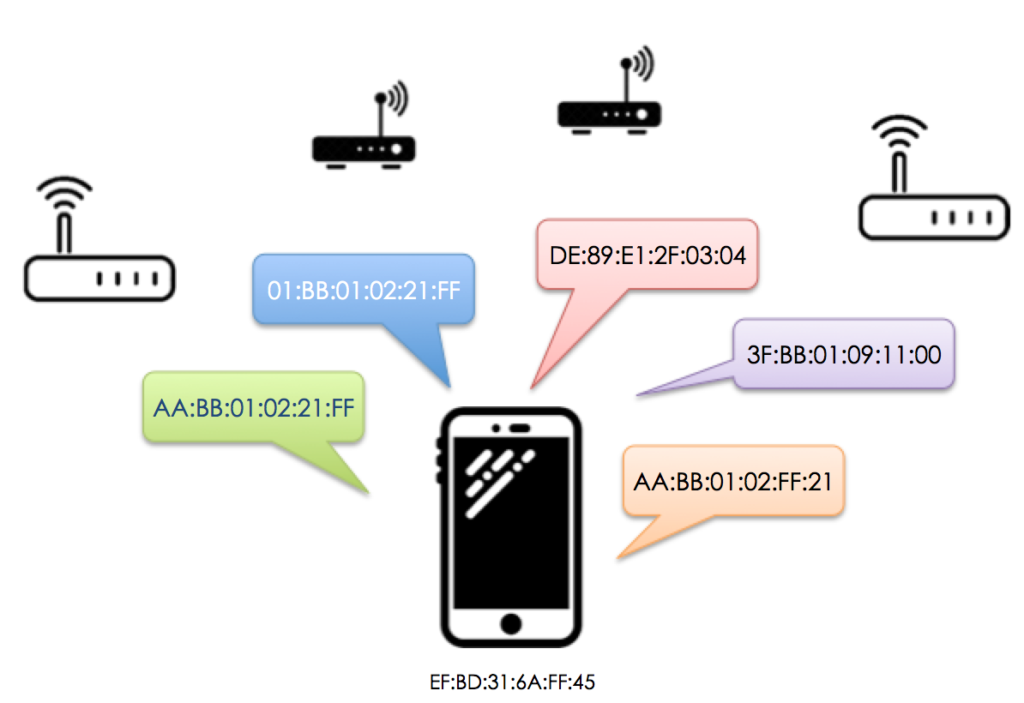
The WiFi protocol requires that transmissions include the MAC address of the transmitting device. However, for probing purposes, many Android and iOS devices are using a variation of the real MAC address when presenting them to unknown networks; this “fake” MAC address is not fixed, rather changes periodically. Under such circumstances, it is said that a MAC address is randomized.
While Apple was the first company to introduce the MAC randomization technique with the release of its operating system iOS 8, in 2014, this method is currently widely used in many Android phones, including Samsung Galaxy S8 and S9, and Google phones. Taking into account today’s market share of the two operating systems combined, the MAC randomization approach involves at least 95% of the new phones in the mobile population.
MAC randomization is nevertheless not identical among all phones: phones from different manufacturers implement the MAC randomization differently, just speaking of frequency and coding.
Phones’ manufacturers claim that one of the main reasons to introduce MAC randomization techniques is to protect users’ privacy, by preventing the tracking of the devices via the MAC address. Despite being hard to tie the MAC address to specific people without any other mean of connection, for marketing and security purposes many tech providers analyse people traffic in shops, airports, conventions, etc. based on phones’ presence and location.
It is still possible to count the number of devices that connect to an access point, yet this amount is only a small fraction of the actual mobile devices in the area, because of the MAC randomization. The overestimation in counting crowds due to such probe requests typically comes in a factor from 2 to 10. The same phone will, in fact, be counted as many times as the number of randomized MAC addresses it transmits to the listening receiver.
There is no way to recover the randomized MAC address. However, it is possible to elaborate alternative approaches making the counting as accurate as possible, given the limitations.
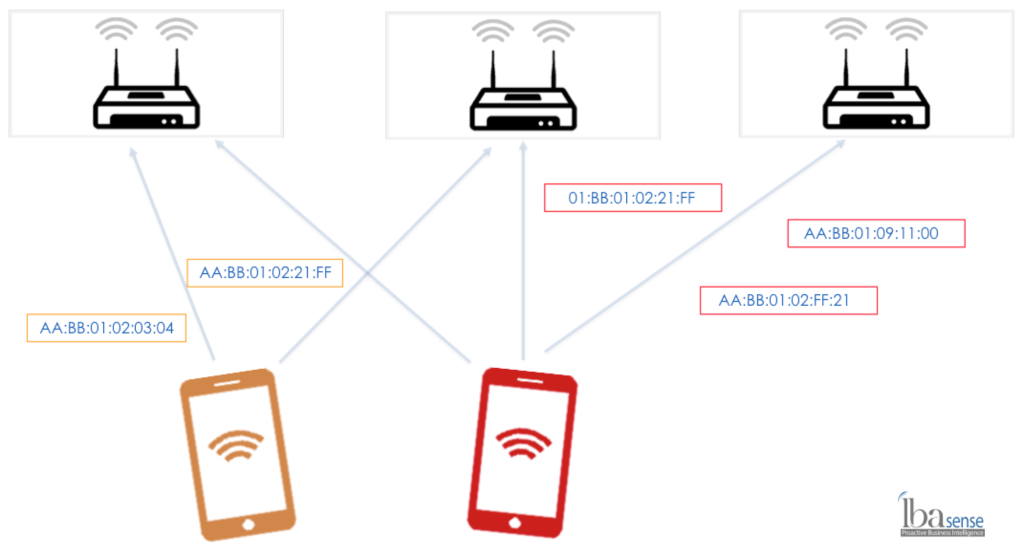
LBASense is able to detect randomized MAC addresses in general and for specific variants of randomization algorithms. By associating multiple MAC randomization messages in groups representing phones, LBASense prevents overcounting.
Based on this patented capability, LBASense system can provide the correct phone counting that includes devices that are using MAC randomization and the ones that are not. As such, keeping its passive and non-intrusive approach, LBASense is the only platform that can use WiFi detectors for people counting, without using factors or assumptions that are hard to justify.
For more information, contact us and we will be happy to help.
Data team
Copyright © 2022 DFRC
43 Science Park Road #01-11 Rm 8, Singapore 117408